Working with a specific static site generator?
Customize CloudCannon's documentation to suit your SSG.
Great! We'll show you documentation relevant to .
You can change this any time using the dropdown in the navigation bar.
Adding a new SSL certificate#
Only sites with custom domains can add custom SSL certificates.
First you need to turn off CloudCannon's autogenerated SSL:
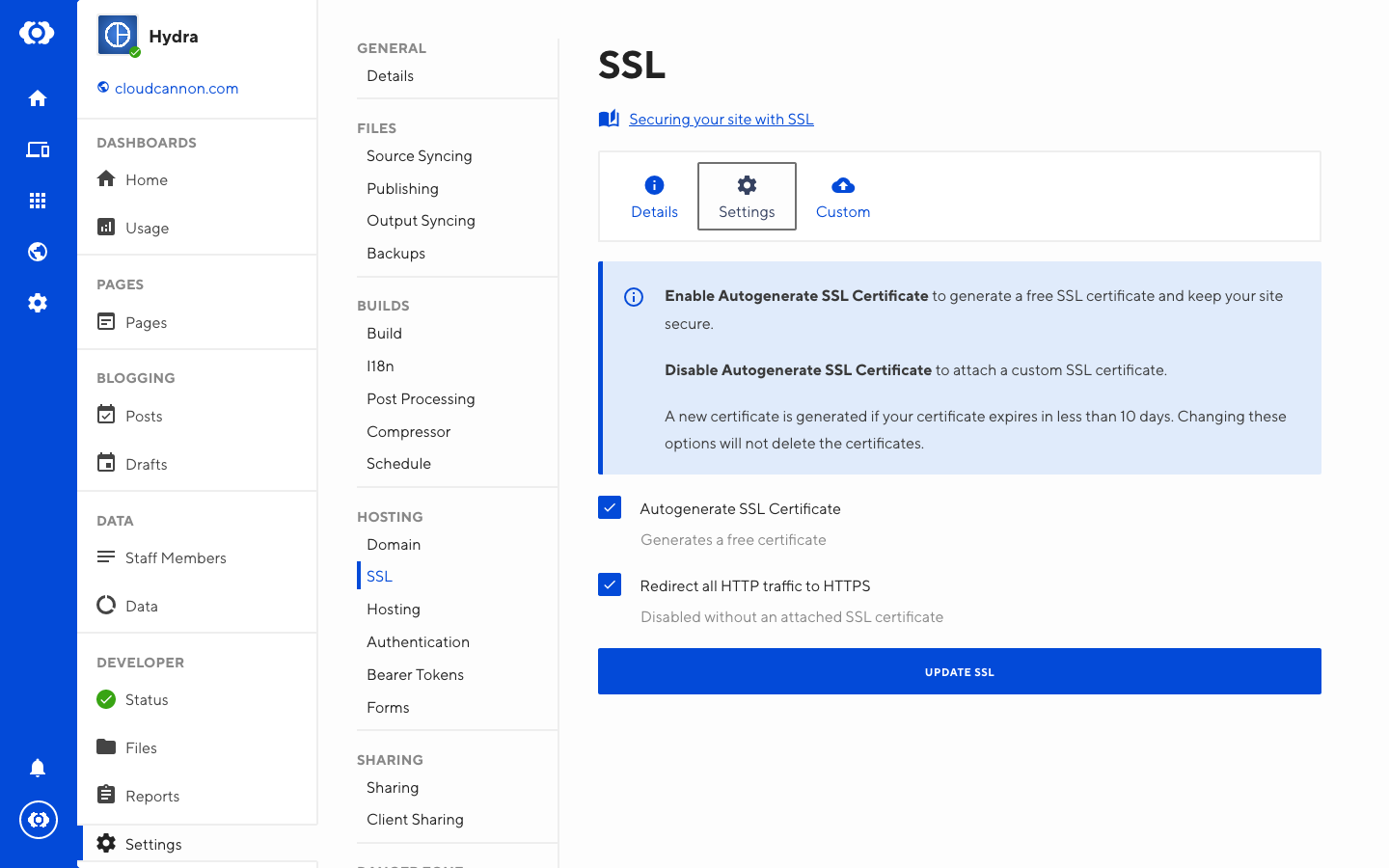
- Navigate to Site Settings / SSL / Settings
- Untick Autogenerate SSL Certificate
- Click Update SSL
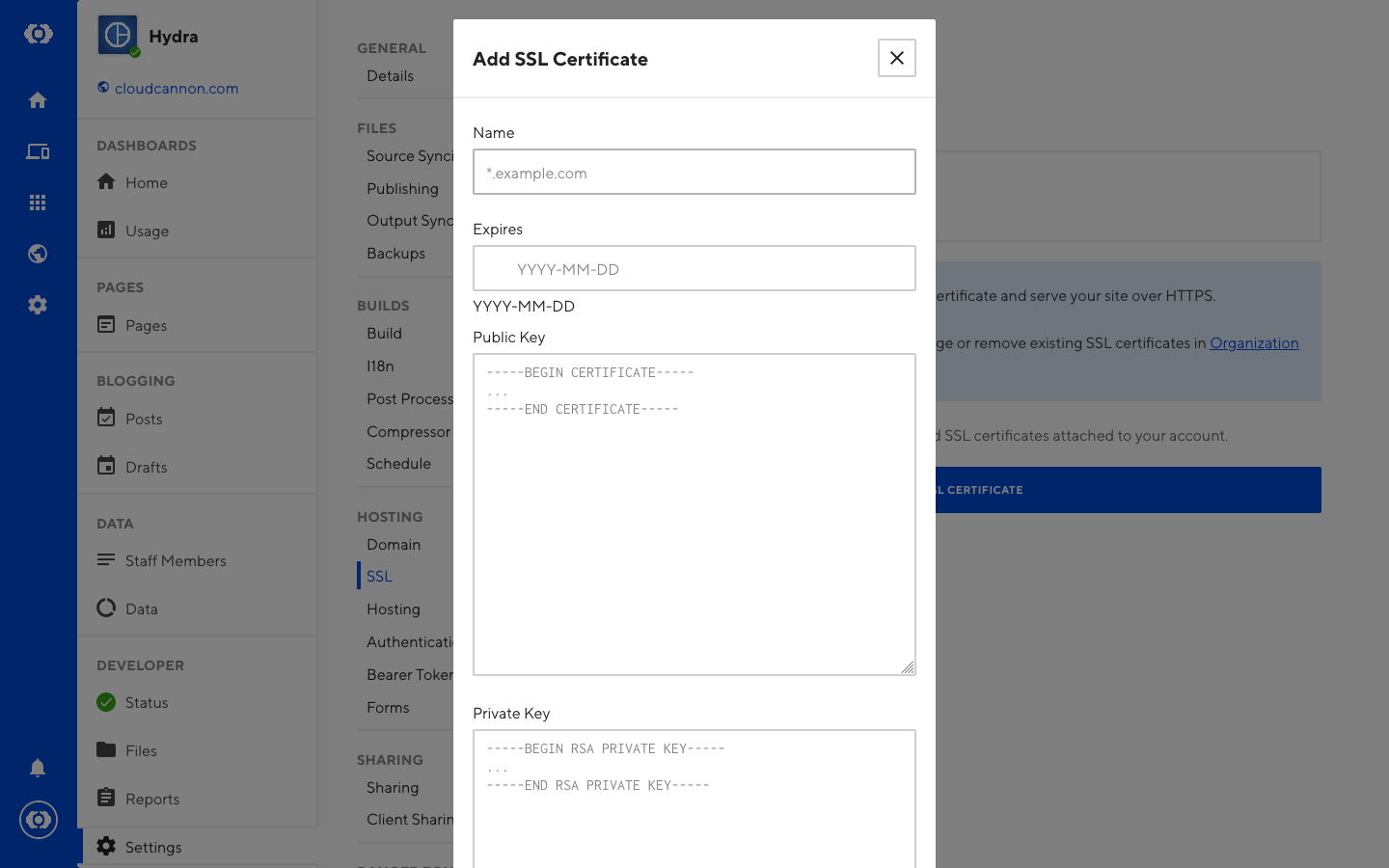
To add a new custom SSL certificate:
- Go to Site Settings / SSL / Custom
- Click the Add SSL Certificate button
- Fill in all of the fields available and submit the form
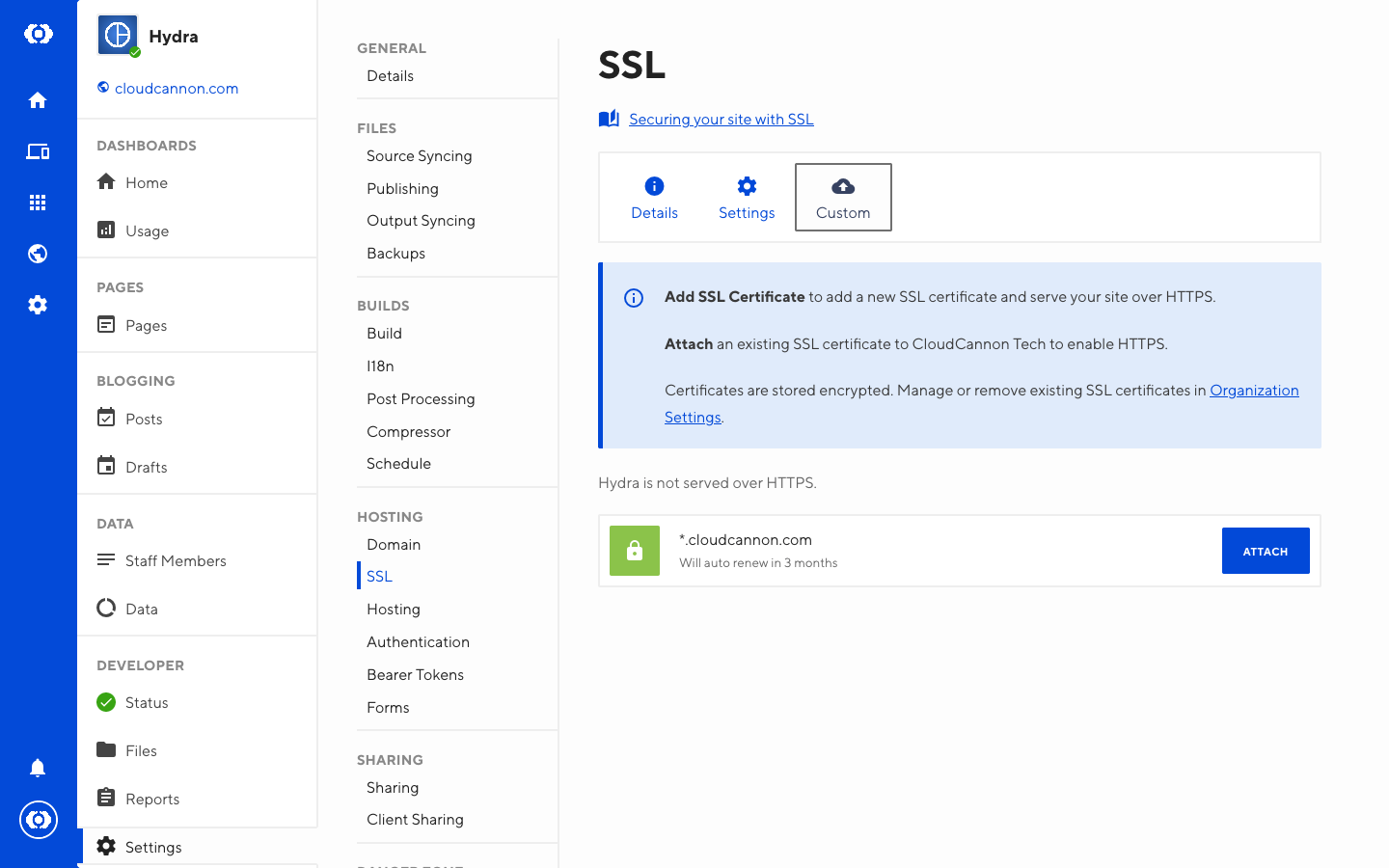
Once added, the SSL certificate needs to be attached to the site.
All certificates must be in PEM encoding. The placeholder text indicates the correct start and end headers.
Attaching an SSL certificate to a site#
To add an existing custom SSL certificate to a site:
- Go to Site Settings / SSL / Custom
- Click Attach on any SSL certificate
Redirecting HTTP to HTTPS#
To redirect all HTTP traffic to HTTPS:
- Go to Site Settings / SSL / Settings
- Enable the Redirect all HTTP traffic to HTTPS option
- Click Update SSL